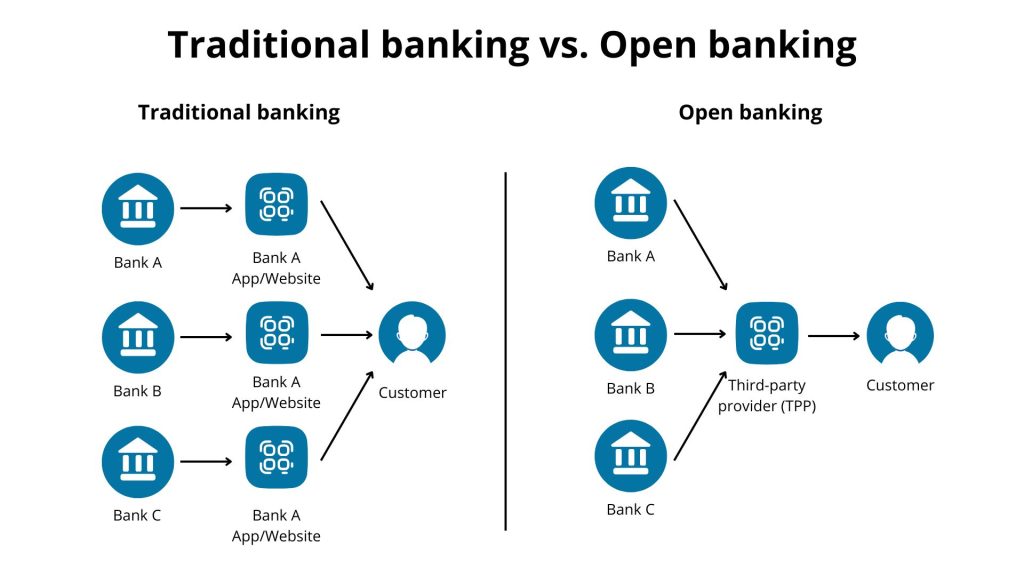
Open banking is transforming the finance industry by breaking down data silos and enabling the secure sharing of data. Traditionally, banks kept customer data locked behind proprietary systems, which made it difficult for outside apps to integrate. Today’s consumers and businesses expect real-time, personalized financial services. Thanks to regulations like PSD2 (EU) and open banking standards in the UK and elsewhere, banks now expose account information and payment APIs to licensed third-party providers. Open banking has become a strategic imperative. A 2023 report projects that the value of global open banking transactions will exceed $330 billion by 2027. For startups and product teams, this means vast new opportunities for innovation in payments, lending, and wealth management, provided they are built securely and pragmatically.
What open banking is (and what it isn’t)
Open banking is a regulated model in which banks (Account Servicing Payment Service Providers, or ASPSPs) provide authorized third parties (Account Information Service Providers, or AISPs; and Payment Initiation Service Providers, or PISPs) with secure API access to customers’ account data and payment services. Access is only allowed with explicit consumer consent. Under PSD2 (EU) and similar regulations, banks publish standardized API endpoints that apps can access to retrieve account balances and transaction history or initiate transfers. For instance, an app could retrieve "read-only" account information or send a real-time payment from the user's account with two-factor authentication.
Open banking is neither screen-scraping nor unfettered data sharing. It is also different from general open data initiatives in that users must expressly permit each data use (often via an OAuth 2.0 consent screen), and banks limit data by scope and timeframe. Compliance is mandatory for regulated banks in PSD2 regions, ensuring that APIs meet security standards. Although "open banking" implies openness, access is actually controlled: only licensed providers and vetted apps can connect. In short, open banking is a secure, API-based method that allows apps to accessbank data and payments under strict privacy and security rules.
How open banking works (high-level flow)
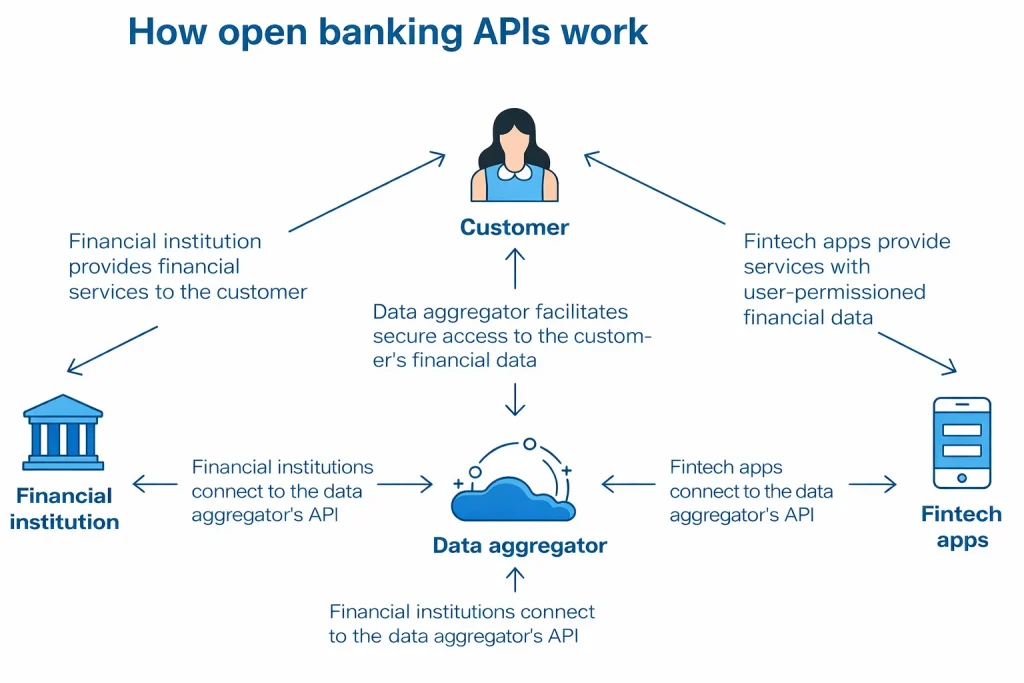
In an open banking flow, three parties collaborate: the bank (account provider), the user (account holder), and the third-party provider (TPP) (app or fintech). The TPP must be registered (or use a regulated aggregator) and follow OAuth2/OIDC-based flows. A typical high-level flow is:
- TPP registration. The fintech obtains a client identity (client ID/secret or dynamic registration) and any required licensing (AISP/PISP). Banks often require that TPPs be registered in a directory and hold a digital certificate (via a trust service provider) for mutual TLS authentication.
- User consent and authentication. In the app, the user selects an account or payment action and is redirected (or shown an embedded frame) to the bank’s secure consent page. The bank authenticates the user (usually via multi-factor Strong Customer Authentication, SCA) and asks them to authorize the specific data access or payment. Once approved, the bank issues an authorization token or code to the TPP.
- Token exchange. The TPP exchanges the authorization code for an access token (and optional refresh token) via the bank’s OAuth2 token endpoint. In open banking, tokens are often sender-constrained (bound to the client via mutual TLS or DPoP) for security.
- API calls. With the access token, the TPP calls the bank’s standardized APIs. For Account Information (AIS), it may call endpoints like /accounts, /balances, /transactions to read data. For Payment Initiation (PIS), it calls /payments to initiate a transfer. All calls are secured (typically via TLS/mTLS) and must include a valid token and idempotency key for payments. The bank validates the request, then returns data or execution status. For payments, the user may also be redirected again to confirm the transaction (another SCA step).
- Consent management. Each access is scoped by the consent: the token encodes which accounts and data types were approved, and how long the consent lasts. Banks and TPPs store consent records so that future calls are valid only under the user’s consent. The user can revoke consent at any time, stopping the data flow.
- Data delivery and updates. The TPP receives the account data or payment confirmation and presents it in the app. Optionally, banks or aggregators may offer webhooks for event notifications (e.g. a new transaction or payment status update). Otherwise, the TPP polls the API for updates, which requires careful handling of pagination and rate limits.
In summary, open banking is a secure API-based handshake: the user logs in at their bank, approves sharing, and the TPP uses OAuth2 tokens to fetch or push financial data. This flow leverages standard web security (TLS) and financial-grade profiles (mutual TLS, sender-constrained tokens) to meet regulatory requirements.
Business value (who benefits and how)
Open banking creates value across the financial ecosystem:
- Consumers and SMBs: They gain richer apps and services. For instance, an SMB can link all its bank accounts to one dashboard, see cash flow and expenses in real time, and initiate payroll payments via bank APIs, eliminating manual reconciliation. Individuals get apps that aggregate accounts and personalize budgeting or saving recommendations. Overall, customers get more control and choice.
- Fintechs and startups: Access to bank data lowers barriers to innovation. Lenders can instantly verify income and spending (cutting approval times), payment apps can move funds cheaply via account-to-account transfers, and wealth managers can offer holistic portfolio advice by pulling in transaction data. For example, with an Income Verification API, a lender and borrower can skip paperwork: the borrower connects their bank, and the service returns categorized deposit history and an estimated salary. This speeds lending decisions and improves underwriting.
- Banks and Financial Institutions: While open banking was driven by regulation, it also opens new revenue streams. Banks can monetize APIs (e.g. charging fees for premium data) and reduce churn by embedding their services in other apps. They gain ecosystem partners who build on their data, expanding distribution. For treasurers and corporate clients, open banking offers streamlined cash management and analytics (e.g. automated AR/AP reconciliation from transaction feeds). Leading banks use KPIs like API revenue and partner activity to track ecosystem value.
- Merchants: Payment initiation (PISP) APIs let merchants accept “pay by bank” checkout. For example, an e-commerce site can direct a customer to authorize a bank transfer right from the checkout, bypassing card rails. This reduces fees (removing 2–3% card charge) and can speed settlement. Merchants with frequent or recurring payments (utilities, subscriptions, marketplaces) especially benefit from faster account-to-account (A2A) flows.
- Regulators and the ecosystem: Standardization and transparency improve security and competition. Regulators benefit from robust audit trails (banks log all API usage) and can set unified requirements (like SCA) across providers. A healthy open banking ecosystem fosters competition, making financial services more efficient for everyone.
In short, open banking unlocks data: account balances, transactions, payees, credit status, enabling smarter products. As one guideline notes, TPPs can use this flow for “spend analysis, credit decisioning, and payments for e-commerce transactions”. It shifts value from closed silos to an interconnected API economy.
Top use cases
Open banking’s use cases span many categories. Here are key examples:
- Consumer finance: Personal finance apps pull data from multiple accounts for budgeting and money management. For example, a user can link checking and credit accounts to an app that categorizes spend, sets saving goals, or finds better loan rates. “Multibanking” dashboard apps let individuals see all their balances and transactions in one place.
Mini-scenario: A young professional uses an app that, with consent, fetches her recent transactions from two banks. The app automatically tags groceries, utilities, and subscriptions, then sends alerts when budgets are exceeded. Over time it even predicts bill due dates from recurring payments. - Lending and credit: Open banking enables instant credit assessment. Lenders (personal or SME) can request a user’s AIS data to verify income and cash flow. This reduces fraud and paperwork. For instance, a small-business loan app might ask an applicant to connect her business account. Within seconds it sees the last 6 months of deposits, automatically categorizes payroll and revenue, and verifies that income matches tax filings. This SME lender can now underwrite a loan in minutes instead of days. Thin-file borrowers (no credit history) benefit too: their bank data provides real context for approval.
- Payments and checkout: Many startups and merchants use Payment Initiation APIs to process transactions. Account-to-account (A2A) payments let customers pay directly from their bank accounts. For example, an online retailer offers “Pay by Bank” at checkout. The customer selects their bank, authenticates, and approves payment. The order is paid immediately with no card involved. The merchant saves on card fees (often >2% of ticket value) and gains security via the bank’s own authentication.
Mini-scenario: A commuter purchases a monthly transit pass. At checkout, she opts to pay by bank. After logging into her bank and completing the SCA, the fare is paid instantly. The transit agency sees the funds immediately on settlement, with no chargebacks or card-breach risk. - Wealth management / Open finance: Investment and advisory firms use open banking for richer advice. A robo-advisor might aggregate all a client’s accounts (checking, credit, investment) to recommend portfolio rebalancing. Open Finance (beyond banking) is emerging: e.g. linking pension or insurance data. Insurers can speed quotes by pulling spending patterns to gauge risk. For example, a personal insurance app could ask to read recent bank transactions to verify a user’s driving-related expenses (e.g. fuel purchases) when pricing a car insurance.
- Enterprise / Treasury: Corporations use open banking APIs for corporate finance. An accounts team can automatically reconcile invoices by matching receivables to actual transactions from the bank. A CFO can connect multiple subsidiary accounts to a treasury app to get real-time cash positions across currencies. Startups also use it for payroll and expense systems: employees submit bank account details via an app for expense reimbursements, and the system initiates payments via AIS/PIS.
Mini-scenario: A global retailer consolidates its bank data (from country banks in EUR, GBP, USD) into one treasury dashboard. When excess cash is detected in one market, the treasurer instantly uses a PISP API to transfer funds to another branch’s account, optimizing liquidity without manual wire transfers.
These use cases are not exhaustive, but they demonstrate the scope of open banking. Open banking generally enables any service that benefits from account information, such as balances, transactions, and statements, or payment initiation, such as A2A transfers. Open banking spans B2C (personal finance apps), B2B (SMB accounting and enterprise treasury), and C2B/C2C (bill payment and peer-to-peer payments).
Software solutions landscape (what to build)
Building an open banking product involves several software components. At a high level, key modules include:
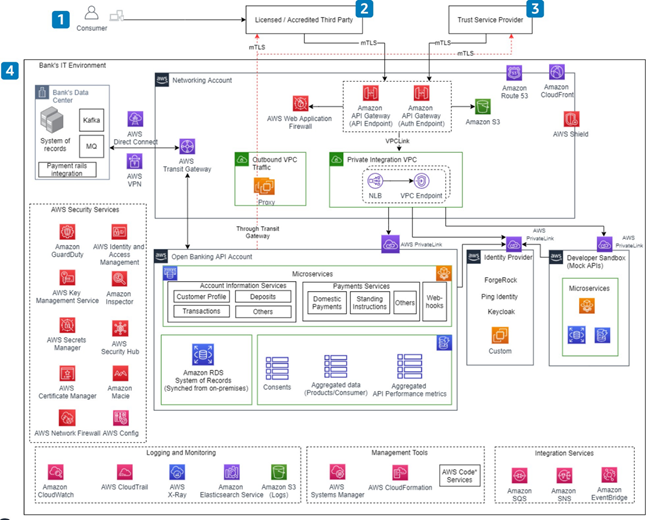
- API Gateway and Developer Portal: This handles all API traffic. It enforces OAuth2.0 (or FAPI) security, mutual TLS, rate limiting, and logging. A developer portal lets TPPs register applications, obtain API keys or certificates, and test calls.
- Identity & Consent Manager: Manages user authentication and consent screens. This service interacts with the bank’s identity provider (often via OpenID Connect) to authenticate the user and record their granted consents (which accounts and scopes). It issues OAuth2 tokens for API access.
- Bank Connectors / Aggregator Interface: The core integration layer to banks. If using direct integrations, you’d build connectors that call each bank’s API endpoints (handling differences in protocol and schema). If using an aggregator, this layer calls the aggregator’s unified API instead. In either case, this component handles token exchange (if needed), API retries, and error mapping.
- Account Information Service: Fetches and processes AIS data. It calls account and transaction endpoints, then parses and stores (or caches) results for use in the application. It may also include transaction categorization and enrichment (e.g. mapping merchant names, identifying salary deposits) to make raw data business-ready.
- Payment Initiation Service: Manages PIS flows. It creates payment requests, handles user redirection for SCA, calls the bank’s payment API, and tracks payment status (polling or via webhooks). It also ensures idempotency: each payment request has a unique key so retries don’t double-charge.
- Consent and Token Store: A secure database that records all user consents, issued tokens (access and refresh), and their scopes/expiry. This is critical for audit and for enabling token refresh without re-authenticating the user each time (within consent validity).
- Audit/Logging: High-grade, tamper-evident logging of all API calls, user consents, and transactions. Because of strict regulations, every data access must be auditable. This includes storing hashes of consent documents and logs of SCA events.
- UX/Front-End: The customer-facing application or web interface that initiates the flows, shows connected accounts, and displays results. It must integrate with the bank’s redirect/OIDC flows and handle loading states while awaiting API responses.
- Analytics and Monitoring: Tracks KPIs (see below) and system health. Open banking integrations involve external APIs that can be slower or rate-limited, so monitoring performance and errors is crucial.
Each solution can be developed internally or assembled from services. Many teams start by using an API aggregator platform, such as open finance SDKs or services, to avoid direct bank integration. Then, they plan to build their own connectors if needed. Others use open-source reference implementations, such as the sample code provided by the UK Open Banking standards, or cloud services designed for open banking.
Regardless of the approach, products must integrate core security services, including an OAuth 2.0 authorization server, certificate management for mutual TLS, and a fraud/SCA provider. In practice, banks often federate to a common trust service provider for certificates, so your system must support that public key infrastructure (PKI).
Check out a related article:
Fintech Cybersecurity Protocols in 2025: A Practical Playbook for Startups & Scale-ups
In summary, a complete open banking platform typically includes an API gateway with FAPI/OAuth2 security, a user authentication and consent manager, bank API connectors or an aggregator client, account data processing, a payment engine with idempotency, and robust logging and auditing. A modular, microservice architecture often works best for separating these components.
Reference architecture (practical, product-minded)
A simplified reference architecture might look like this (components in rough order of flow):
- Client App: Invokes open banking features (e.g. "connect bank account" button).
- Consent/UI Service: Redirects user to Bank’s OAuth2 authorization endpoint for login/SCA.
- Authorization Server: Bank’s or own server issuing tokens upon successful login.
- API Gateway: Receives calls from the Client (with access token) and routes them securely.
- Account Service: Backend that calls the bank’s AIS endpoints and returns account data.
- Payment Service: Backend that calls the bank’s PIS endpoints to send payments.
- Consent Store: Database of user consents and token states.
- Logging/Audit: Captures every request, consent action, and response for compliance.
This flow follows AWS’s open banking reference: after user consent, the TPP (third party) retrieves account info or submits payments. The AWS lens emphasizes that “Data is shared to third parties only after consent from the customer using OAuth2.0” and that all third-party access should use mutual TLS for security. In practice, you’d enforce mTLS at the gateway and use FAPI’s sender-constrained tokens to bind tokens to the client.
For a product team, the emphasis is on building usable, secure services. For instance, the Account Service might cache recent transactions and categorize them (since banks often return raw data). The Payment Service must implement idempotency keys and async status tracking (banks may process payments with a delay). All services must validate the scopes in the access token against requested data: e.g. do not fetch transactions if the token only covers balances.
Integration approaches: direct vs aggregator vs hybrid
When building open banking connectivity, teams generally choose one of three paths:
- Direct (Point-to-Point) Integration: The company becomes a licensed AISP/PISP and directly integrates with each bank’s API.
Pros: Maximum control over flows and data; no dependency on third-party providers.
Cons: Regulatory burden (you must get authorized), high upfront effort, and each bank has its own integration and maintenance. You’ll need to build and maintain separate connectors per bank and handle local compliance. This path makes sense if you plan a major open-banking-based business. Advice: Only large fintechs or banks usually take this road. For most startups, it’s often better to start with an aggregator. - Aggregator (Licensed Third Party Service): Use an open banking platform (e.g. Plaid, TrueLayer, Yodlee, etc.) that already connects to many banks. You build only one integration to the aggregator’s API.
Pros: Fast time-to-market and broad coverage (dozens of banks at once); the aggregator handles token exchanges, varying protocols, and some compliance.
Cons: Ongoing fees (often per API call or volume), potential vendor lock-in, and less visibility into the low-level APIs. You may also need to check if the aggregator is regulated: sometimes you can piggyback on their license, but in other cases you still need your own PISP/AISP license depending on the use case. Many products launch on an aggregator for MVP, then consider direct connections later for scale. - Hybrid: A mix of both. For example, you might integrate directly with the country’s largest banks for guaranteed connectivity and use an aggregator for additional banks or regions. Or you might use an aggregator for AIS (data) but build your own PIS (payments) integration for greater control over checkout flows.
Pros: Balance of coverage and control.
Cons: Complexity increases: you must manage two different systems and merge their data. Careful architecture is needed to handle concurrency and which source is “true” for each piece of data.
In practice, you might decide based on coverage needs and resources. If you only need one or two local banks, direct could work. If you need dozens (especially globally), an aggregator is practical. Consider a quick decision matrix:
- Budget/Time: Aggregator wins (less dev effort). Direct needs heavy investment.
- Control/Customization: Direct wins (you own flows). Aggregator is more one-size-fits-all.
- Compliance: Aggregators often have compliance infrastructure; direct requires you to do it yourself.
- Coverage: Aggregators cover many banks; direct requires building each.
- Vendor Risk: Aggregator creates dependence; direct avoids lock-in.
- Hybrid: Good if you have mixed needs (e.g. direct for critical flows, aggregator as fallback).
A Yaspa blog notes: “Working with an aggregator allows you to start with open banking more quickly, but product development is still necessary… Depending on the regulatory status, you may still need to be regulated as a PISP or AISP.” Conversely, building your own “is resource-intensive, but it provides complete control”. Choose based on your core competence: if your team is strong in bank integration and compliance, direct may pay off in the long run. If you need to launch fast with limited team size, an aggregator or end-to-end service is prudent.
Compliance, privacy, and risk (non-negotiables)
Open banking is heavily regulated. Security and privacy must be built in from day one:
- Strong Customer Authentication (SCA): All customer-initiated flows require 2-factor authentication. Practically, this means your app must redirect users to their bank’s own authentication (OTP, biometric, etc.) whenever they grant consent or initiate a payment. No workaround is allowed. Ensure your UX accommodates these extra steps gracefully.
- OAuth2/FAPI Security: Use the Financial-grade API (FAPI) profiles of OAuth2.0/OIDC. This means using mutual TLS or DPoP to bind tokens to the client app, using short-lived tokens, and employing pushed authorization (PAR) if supported. Never send tokens in URLs, always over HTTPS. Follow best practices for certificate pinning and key management.
- Consent Management: Log and enforce user consent explicitly. Each access token must correspond to an active consent with clear scope and expiry. Allow users to view and revoke their consents. Store consents securely (e.g. hashed records) and tie every API call to a valid consent entry. Under GDPR, the consent for data access must be “freely given, specific, informed, and unambiguous,” so document this. Banks and regulators may audit your consent records.
- Data Privacy (GDPR, etc.): Only collect and store the data you need. Encrypt data at rest and in transit. Comply with GDPR and similar data laws: allow data deletion requests, restrict cross-border transfer as required, and minimize personal data. Remember that transaction data can contain sensitive info; treat it like healthcare data in terms of security.
- Certificate Management: In many open banking regimes, TPPs must use X.509 certificates to authenticate (via mutual TLS). You may need to obtain and rotate certificates from a Trust Service Provider. Manage these through an automated PKI process if possible.
- Resilience and SLAs: Banks expect high availability. Follow operational guidelines (like UK’s performance standards). Implement retries, backup plans (e.g. fallback payment channels), and support for error scenarios. Log failures in detail for debugging.
- Fraud and Risk: Incorporate fraud detection and AML checks as needed. While the bank authenticates the user, you should still monitor for unusual usage (e.g. a user suddenly connects dozens of accounts). Use identity verification (A2A can serve as a form of bank-backed KYC) and transaction anomaly detection if you handle large volumes.
- Audit and Logging: Maintain immutable logs of all actions. Regulators often require both a raw API call log and proof that consent was given. Log challenge/responses and IPs. Ensure logs are tamper-evident.
Non-negotiable: trust. Every customer must trust that your app handles their financial data safely. Follow security profiles and guidelines (e.g. UK OBIE Security Profile, PSD2 RTS) as baseline. Regularly perform security reviews and keep abreast of new PSD2/PSD3 updates. Compliance is not an afterthought – it’s central to product design.
Implementation roadmap (MVP → phase 2 → phase 3)
A pragmatic build plan breaks work into stages:
- MVP: Focus on a single use case and minimal scope. For example, an MVP might only support AIS (reading account balances) via one major bank or one aggregator. Use an aggregator (if available) to simplify integration. Build the OAuth2 flow for one bank, store consents, and display account info. Skip advanced features (no categorization, just raw transactions). Ensure SCA and consent flow works. At this stage, prioritize reliability of the core flow. Don’t worry about multi-bank or multi-currency yet. Common pitfalls: underestimating the complexity of OAuth flows (test thoroughly), forgetting idempotency on payments, or not handling user-denied consents gracefully.
- Phase 2: Expand functionality and coverage. Add more banks and regions. Support both AIS and PIS if not already. Implement data enrichment (transaction categorization, merchant lookup) to make data user-friendly. Add more UI features (historical charts, notifications on new transactions, etc.). Improve the consent dashboard (let users manage connected accounts). Start automating certificate rotations and compliance reporting. If using an aggregator, evaluate whether to build direct connectors for high-volume banks (to reduce costs or improve uptime). Enhance security posture (e.g. rotate keys, implement anomaly detection). Monitor and refine KPIs (see next section).
- Phase 3: Scale and optimize. Offer multiple products (e.g. introduce savings/loan offers, or expand to open finance beyond banking). Integrate additional open finance data sources (investments, pensions, insurance) as APIs become available. Support advanced payment types (future: recurring Variable Recurring Payments or international transfers). Automate scaling (cloud deployment, containerization). Implement SRE practices for high availability. Potentially globalize the offering (multi-currency, comply with non-EU open banking standards). Continuously update to new regulatory requirements (like PSD3 or Open Finance mandates).
Throughout all phases, keep a tight feedback loop with users. Open banking is new to many end-users, so clear instructions and robust error messages are critical. Always test SCA flows on real bank sandboxes. Common pitfalls include not properly handling certificate or API changes from banks (they do update specs), and over-engineering too early (build simply, refine iteratively). Focus on delivering actual business value (e.g. “Did we actually verify income faster?”) rather than chasing every possible feature at once.
KPIs to measure success
Tracking the right metrics ensures your open banking product is working:
- User Adoption: Number of users (or accounts) connecting via open banking. Track monthly active users (MAUs) of the open banking feature. For fintech apps, link this to overall growth. Growth in MAU shows whether the feature drives engagement.
- API Usage: Calls per day/week to account and payment APIs, and success/failure rates. A high success rate (>95%) means your integration is stable; a surge in failures may indicate a bank outage or bug. Monitor average response times. If using an aggregator, track calls by country or bank to identify coverage gaps.
- Consent Metrics: How many consents created vs revoked? A high consent dropout could mean the flow is confusing or not trusted. The consent renewal rate (users continuing to re-authorize) reflects satisfaction.
- Business Metrics: If monetized, measure revenue from API usage or subscriptions. For payments, track total volume and value processed via PISP vs traditional channels (e.g. card). For example, one KPI is the ratio of bank payments to card payments. For lenders, measure how much faster loans close (e.g. average approval time with open banking vs old method).
- Data Quality: If you provide enriched data (categories, merchant info), measure coverage (percentage of transactions automatically categorized). Low coverage indicates a need to improve algorithms or data sources.
- Operational SLAs: Monitor system uptime and latency. Open banking features usually have SLAs (e.g. 99.5% uptime). Track Mean Time to Recovery (MTTR) for incidents, and bug counts per release.
- Customer Experience: Surveys or support tickets specifically about open banking features can reveal friction points (e.g. “It took too long to connect my account”). Churn rate comparison: are users who enable open banking more likely to stick around?
- Fraud/Mistrust Signals: Unusual spikes in declined consents, or reports of unauthorized charges (even if rare) should be tracked closely. These are indirect indicators that something needs fixing.
In summary, combine technical KPIs (availability, success rates, latency) with business KPIs (user adoption, transaction volume, revenue) and UX KPIs (MAU, consent renewals). This ensures you measure both the platform’s reliability and its real business impact.
Conclusion (actionable next step)
Open banking opens a world of innovation but comes with responsibilities. Next steps for teams new to open banking:
- Pick the first use case and tech approach. Start with the simplest high-value flow (e.g. account aggregation for budgeting, or pay-by-bank checkout) and decide direct vs aggregator based on resources. Get a sandbox account and run through the OAuth flows early.
- Ensure compliance from day one. Consult PSD2/OBIE/FAPI specs as you design. Build your security and consent layers first – it’s much harder to bolt them on later.
- Prototype quickly, then iterate. Use existing libraries or API platforms to shorten dev time. But keep a path open to optimize or replace them as you grow.
- Measure and adapt. Use the KPIs above to guide improvements. If users drop off at consent, improve the UI; if payments fail, troubleshoot APIs or switch endpoints.
- Plan for scaling. Even in an MVP, choose architectures (cloud, microservices) that let you add new banks, currencies, or apps without rewrites.
Ultimately, the actionable next step is to define your MVP: choose a use case, scope (AIS or PIS), and integration route, and build a minimum end-to-end flow (auth, consent, one API call) to validate the concept. Once that’s working, you can expand coverage and features. Open banking is a journey: start small but think big, and build on solid, secure foundations.
Leave a Comment